Email is not private. Ever.
We’ve heard a lot about email security during this election year and I am afraid people may have gotten some wrong impressions from the discussion. Most of the debate has been over the use of secure email servers. People may get the impression that using a secure email server makes the information on email private. Securing an email server makes it difficult to snoop into email stored on the server, but that is only a fragment of the picture.
Using email for critical private information is unwise under any circumstances. I fear this point is lost in the discussion. An email server is only one vulnerability in the chain of vulnerabilities from sender to receiver. You can never be certain, even reasonably sure, they are all safe.
Sending information in an email exposes the information to unauthorized access that you will not be able to control. In addition to unauthorized snooping, any email sent or received on company email is open to both the employer of the sender and the receiver. A business may be legally required to make their email public in court. An additional danger is the email message you receive may not be the message your correspondent sent to you. The sender in the email header may not be the real sender. Email was designed for convenience, not for integrity or privacy of communications.
My attitude, and that of a few other software and network architects with whom I have discussed it with recently, is to treat an email as a postcard, open to anyone who cares to snoop.
How email snooping works
To understand email security, you have to know a little about the email system architecture. There are five components: the email sending client, the receiving client, the connecting infrastructure, and the sending and receiving servers. Usually the sending and receiving clients are a single piece of software, like Outlook or Thunderbird, but the sender and receiver each has their own. In addition, unless you are sending email to someone in your own domain (the right side of the “@” in both addresses are the same) the email will go from the sender’s client to the sender’s email service to the receiver’s email service to the receiver’s client. The connecting infrastructure is usually the Internet, and it is often the most vulnerable part of the process.
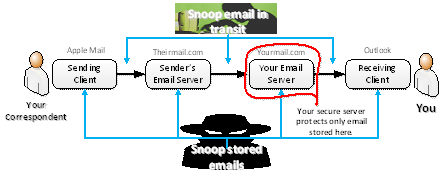
As an email sender, you can protect your email client by choosing a reputable email service, managing your email account passwords carefully, and following good security practices on the devices you use for sending and receiving email, but you do not control the receiver’s elements in the chain. Steps can be taken to increase the security of email, but there is no way to tell if they have been taken at the links you do not control in the chain. In other words, no matter how careful you are, there are still many opportunities for tampering with the email you send and receive.
Email encryption
However, you can do something to protect your privacy: you can send encrypted messages that you encrypt yourself and your recipients must decrypt themselves. Independent encryption that is controlled by you and your recipient eliminates most of the issues. The problem is that you can’t send an encrypted message to just anyone because you and your recipient have to share some secret key to the encryption. This is the method behind PGP (Pretty Good Privacy) that technical types have used for a long time for email privacy. Many off-the-shelf products require less technical skill to use than PGP, but senders and recipients still have to share some secret information before communication can take place. Off the shelf products can hide the sharing and lessen the pain, but you and your correspondents will still have to agree on tools and keys before you can exchange messages privately.
Encrypted email is the only kind that I consider secure. But I also keep in mind that encryption-based systems are still fallible. What is safe today may be vulnerable tomorrow because all encryption can be broken if sufficient computing power is applied. Today, breaking the most secure encryption requires decades of computer time, but tomorrow’s computers are likely to be much more powerful. Emails that are securely encrypted today will be easy to hack in a few years. Also, if an encryption key gets into the wrong hands, the message is no longer private. If a careless recipient saves an unencrypted copy of a message, it is no longer private. Also, a strong but poorly implemented encryption is still weak. Encryption products that ought to have been secure have turned out to be insecure through implementation errors. Always keep in mind that email places whatever you send into the hands of strangers.
Email was, like the Internet, designed for flexible and open communications. Its complex and sprawling structure changes slowly. Computer and network security in general has improved greatly in recent years, but the criminals have gotten better too.
The upshot is that secure email servers do not secure email. I, and many other software engineers and architects, regard all email as insecure. Period. Always assume that hitting the send button makes the message public.
Email is fast and convenient, but not private.